GuardDog’s Solution
61
of mid-sized businesses do not have dedicated cybersecurity experts in their organization.
47
of mid-sized businesses do not currently have an incident response plan.
90
of organizations CANNOT detect, contain or resolve cyber security threats within a hour.
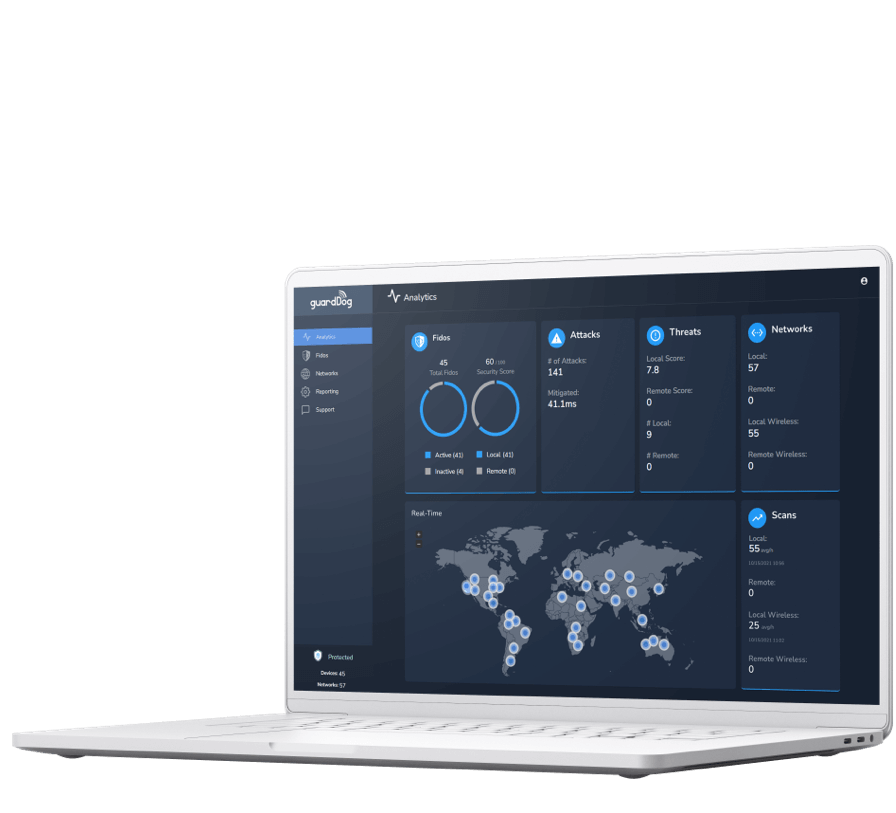
Protective Cloud Service (PCS)
Simple cybersecurity analytics platform
The Protective Cloud Service provides detailed analytics on as many environments as Fidos or VIRTUAL Fidos are deployed.
- Shows existing risk factors with anything on the network
- Shows traffic coming through ANYTHING on the network besides websites
- Allows the customer to see and respond to where they are coming from in REAL TIME
- Provides visibility across one or as many networks as desired
- Makes the PCS fit the individual needs of your organization
- Automated, interrupted countermeasures, and notifications to protect networks and devices from attacks
- AFFORDABLE cybersecurity analytics
- Avoids costly hacks
- Prevents potential attacks and companies possibly going out of business
Protective Cloud Service (PCS)
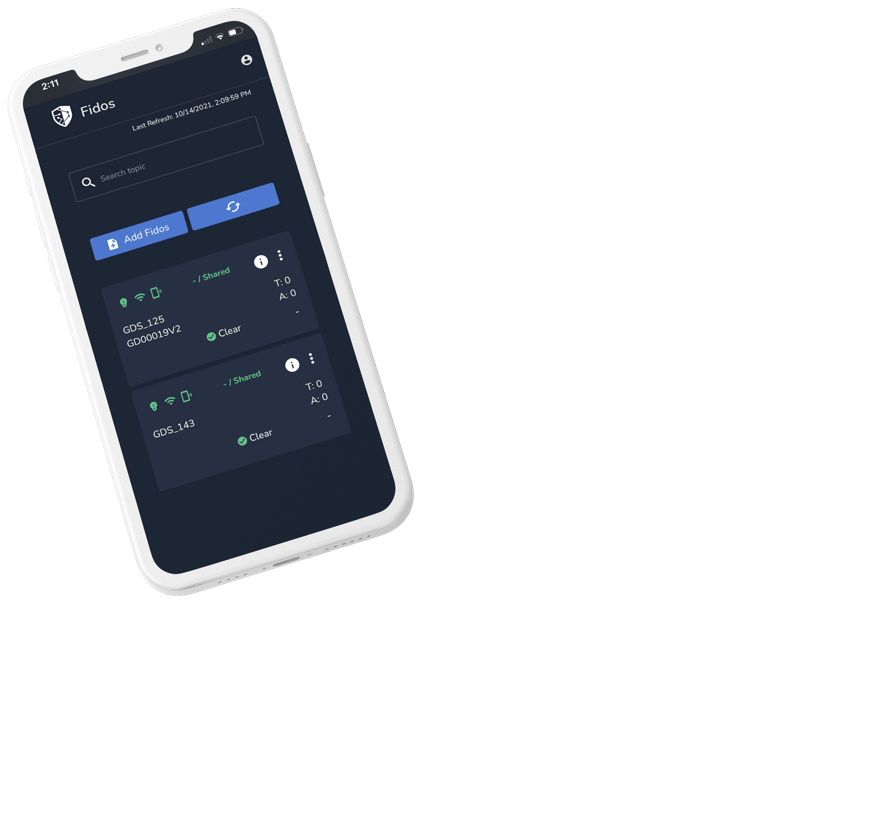
Fido


Protective Cloud Service (PCS)
Virtual Fido
Perfect for Small and Medium Sized Business
Our cloud-service works together with a network security device to protect your networks and devices, 24/7. Protection begins from the moment you plug it in.
Automatic Detection and Response to Attacks
Intelligently Acts as Your Virtual Cybersecurity Expert
Reports Threat Levels to Reduce Risk of Losses

Ultimate Cybersecurity Solution
Hackers Rarely Take a Break, We Never Do
The average hacker can break into a vulnerable network in a few minutes, we stop attacks in milliseconds. Regular scans are made of your network and devices to automatically stop threats and to find vulnerabilities that can be fixed before they are exploited by hackers. With our distributed version, you can protect multiple locations, remote employees, and more.
Frequently asked questions?
Why choose GuardDog?
You can always know how secure you are on any size network or environment.
How quickly will I recognize I am under attack?
GuardDog will notify you instantaneously and will also interrupt the attack from being successful.
Why are GuardDog analytics so effective?
It’s the only one simple enough to be deployed in any environment regardless of complexity or size. Minimal technical knowledge required to interpret the source of the issue.
How do I manage my score?
With the simplified analytics we provide, IT resources with sufficient knowledge will be able to respond. Our support team is ready to help anyone.

